Cyber Security Principles
Introduction
Section titled “Introduction”Information security is the set of practices, processes, and controls designed to protect data from unauthorized access, misuse, improper disclosure, alteration, destruction, or unavailability.
In short, it ensures that a message is forwarded from a sender to a receiver without any interception or modification along the way.
Another terms may also be used, such as:
-
Digital Security;
-
Data Security;
-
Cybersecurity.
For this to be possible in the current times, this protection must comply with certain principles, also called “pillars”, represented in the image below:
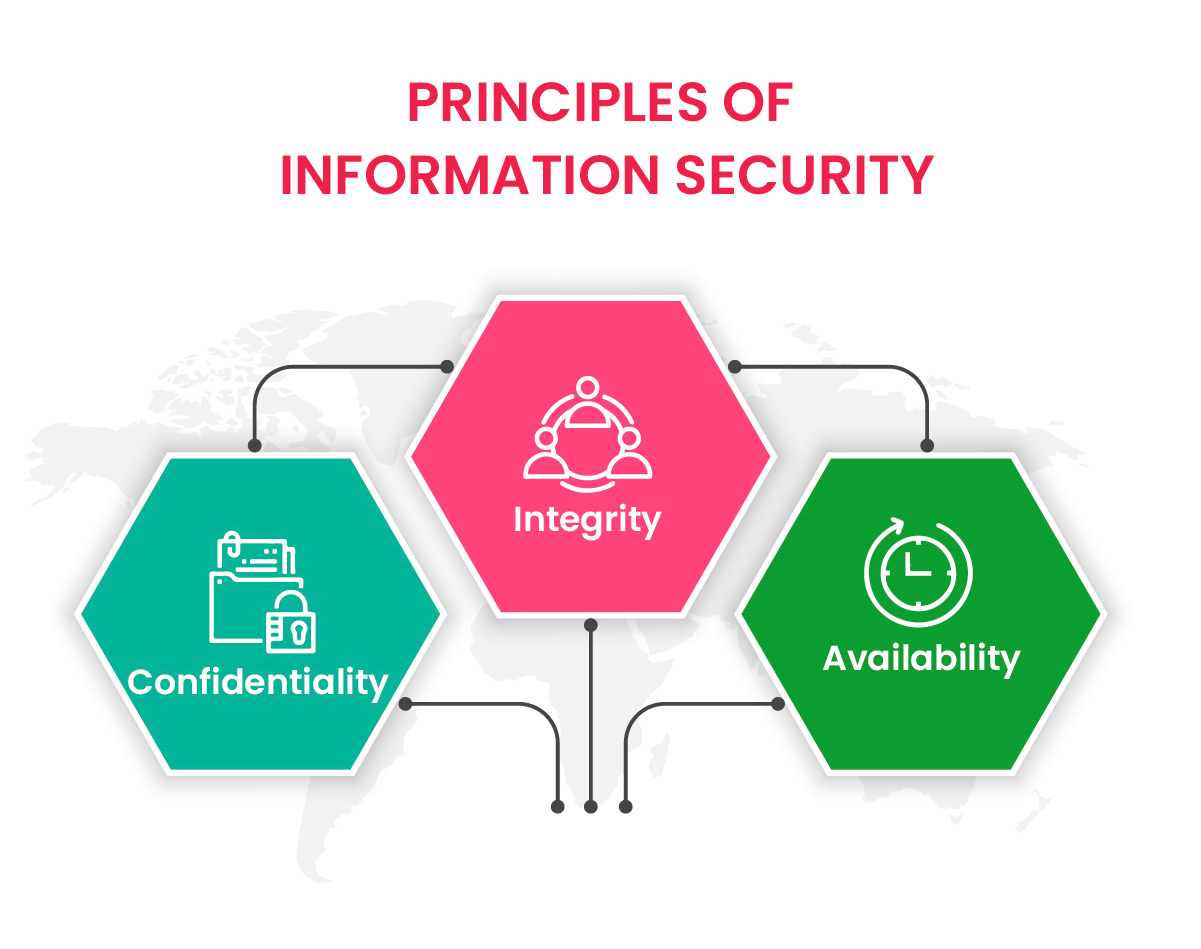
1. Confidentiality
Section titled “1. Confidentiality”This principle ensures that a message sent from sender X should only be received by recipient Y. It also ensures the necessary restrictions on who should have access to this confidential information.
Example: The password used to access a banking application should only be shared between the account holder and the entity that holds their banking information. Other than that, access to this type of information should be considered completely restricted.
Consequence: If an attack on the internal customer registration system allows passwords to be exposed, this confidential information will be exposed to people who should not have it.
2. Integrity
Section titled “2. Integrity”This principle ensures that the information sent will reach the receiver in its entirety. Basically, it is when a message is not altered from the sender, traveling through a channel, and reaching the receiver.
Example: An attacker alters the amounts on an invoice within the company’s financial management system.
Consequence: The data no longer reflects reality, compromising decisions and official records.
3. Availability
Section titled “3. Availability”This principle aims to ensure that information is available to users, regardless of when or where they need it.
Example: A ransomware attack encrypts all files on a server, preventing access to corporate systems.
Consequence: Users and services become unavailable, interrupting critical operations.
New Principles:
Section titled “New Principles:”4. Authentication
Section titled “4. Authentication”Verifies the identity of users or devices to ensure they are who they claim to be, often using passwords, two-factor authentication, or biometrics.
Example: A malicious user forges another employee’s credentials and accesses the system while impersonating them.
Consequence: The system believes the false identity is legitimate, enabling unauthorized actions.
5. Non-repudiation
Section titled “5. Non-repudiation”Provides proof that a user or system cannot deny having sent a message or performed an action, which is crucial for transactions and legal accountability.
Example: A customer performs an online transaction but later claims they never did it, and the system lacks proper records (such as logs or a digital signature) to verify the action.
Consequence: It becomes impossible to prove who carried out the operation, opening the door to fraud or disputes.

